Understanding Shadow AI and Its Risks
Artificial intelligence has become a force multiplier for enterprises, accelerating workflows and unlocking data insights. At the same time, it introduces new risk vectors that many organizations are still trying to comprehend and control.
Why Shadow AI Exists
Employees seek efficiency. When official AI tools are slow, unclear, or unavailable, they turn to public AI assistants (e.g., ChatGPT, Copilot, Gemini) to solve immediate problems. This behavior creates a gap between policy and practice, allowing shadow AI to take root.
Real‑World Example
A developer under pressure copies proprietary code into a public AI assistant for troubleshooting. The assistant returns a solution, the task is completed, but the code may be stored or learned by the external system, potentially exposing sensitive intellectual property.
Current Landscape and Statistics
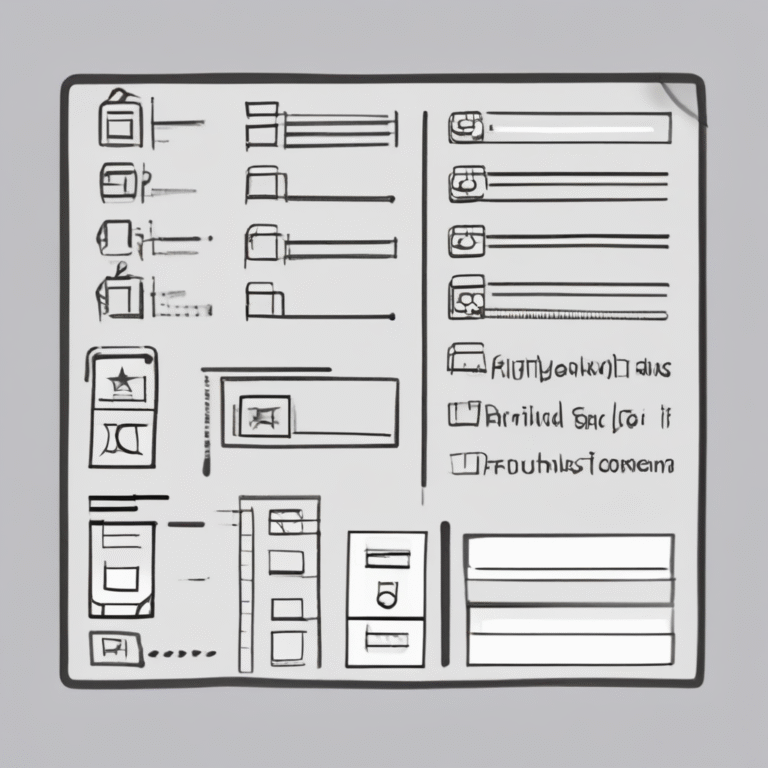
Recent research shows:
- 72% of organizations are concerned about AI’s impact on compliance (up from 58% a year ago).
- 36% still lack an AI compliance policy.
- Over 50% of data breaches in 2025 involved compromised credentials, which can be exploited by shadow AI usage.
- 77% of companies plan to pursue an AI certification within the next 12 months, with 60% favoring ISO 42001, 50% using self‑assessments, and 56% adding AI controls to existing assessments.
Key Challenges for CISOs
Shadow AI poses several challenges:
- Data leakage through unvetted third‑party tools.
- Use of personal accounts for work‑related AI interactions.
- Unmonitored API connections between external AI services and internal systems.
- Difficulty tracking and enforcing regulatory obligations.
Impact of Governance Gaps
When compliance strategies are missing at the executive level, inconsistent and risky behavior spreads throughout the organization, making it harder to detect and mitigate shadow AI activities.
Strategic Priorities for the First 90 Days
1. Establish Accountability
Define clear ownership of AI governance across security, compliance, and business units to prevent effort stagnation.
2. Create Visibility
Inventory all AI usage—both approved and shadow—to understand where employees are turning for assistance.
3. Assess and Prioritize Risk
Identify high‑risk AI use cases (e.g., handling sensitive data) and address them first.
4. Conduct an Audit Partner Assessment
Analyze regulatory, reputational, and compliance risks associated with each AI deployment.
5. Implement Interim Controls
Introduce guardrails for high‑risk activities even before formal policies are finalized.
Policy and Culture: The Dual Pillars
Technology alone cannot solve shadow AI. Effective mitigation requires both policy enforcement and a supportive organizational culture.
Defining Acceptable Use
Employees need clear guidance on what data can be processed with AI tools and under which contexts.
Providing Real‑World Training
Use scenario‑based training (e.g., debugging code, summarizing documents) to illustrate safe versus unsafe AI practices.
Offering Approved Alternatives
When secure, vetted AI tools are readily available, employees are far less likely to seek shadow solutions.
Reinforcing Accountability
Make it explicit that AI usage is part of the organization’s broader security posture, not an exception.
Conclusion
Shadow AI reflects a misalignment between corporate AI policies and employee workflow needs. Closing this gap demands a proactive, transparent strategy that blends governance, education, and accessible tools. By establishing clear accountability, gaining visibility into AI usage, and fostering a culture of responsible innovation, CISOs can turn AI from a potential nightmare into a secure, productive asset.