New Security Exposures of Rapid GenAI Adoption That Organizations Must Address
Generative AI (GenAI) has rapidly evolved from a curiosity to a central force in enterprise technology. Its ability to generate text, code, images, and insights on demand has made it indispensable for employees eager to cut through complexity and accelerate productivity. However, with this innovation and efficiency comes massive exposure to risk.
In discussions with executives and AI governance leaders across industries, a recurring theme emerges: data security has transitioned from a key concern to the focal point of strategic planning and is now the defining challenge of AI adoption. Unlike traditional software or previous waves of machine learning, GenAI fundamentally alters the process for securing data within an organization.
Challenges Faced in GenAI Adoption
Recent studies from MIT indicate that 95% of enterprise GenAI pilots are failing, not due to technological shortcomings, but because enterprises lack the governance and security frameworks required to operationalize GenAI responsibly. Furthermore, enterprise leaders have identified data security as the top business and security risk hindering faster AI adoption.
Additionally, the phenomenon known as shadow AI, characterized by unsanctioned employee use of public tools, has emerged as a significant driver of escalating data risks beyond corporate control.
Least-Privilege Access vs. GenAI
The least-privilege access model grants users, programs, or processes only the minimum level of access required for their legitimate functions. However, GenAI disrupts this paradigm; it thrives on access to more business data and context, which conflicts with the least-privilege principle. Without a clear understanding of how GenAI will be used, setting up appropriate access permissions becomes challenging.
GenAI Exposures to Consider
GenAI expands the data surface, complicating enterprise data governance and security in several interconnected ways:
- Input Leakage: GenAI can ingest raw data, including sensitive business information. Employees may inadvertently feed prompts that contain customer PII, intellectual property, and financial forecasts.
- Output Exposure: Generative models synthesize data, potentially exposing sensitive insights without proper clearance. Outputs may even hallucinate data that appears legitimate but is derived from sensitive training material.
- Accessibility Without Oversight: GenAI tools are embedded in various platforms, allowing employees to adopt them instantly and bypass governance, which fuels shadow AI.
- Second-Tier Supply Chain Risk: Vendors may rely on subcontractors that introduce their own data handling policies, increasing the risk of sensitive data being mishandled.
- Governance Gaps in Training Data: Once data enters an AI model, enterprises lose control over how it is used, complicating retraction efforts.
- Application Code Risk: Developers using GenAI tools may unknowingly introduce vulnerabilities or license conflicts into business systems.
Addressing GenAI Risk
With GenAI already embedded in enterprise workflows, organizations must adopt it responsibly to avoid costly breaches, regulatory penalties, and reputational damage. Blocking GenAI outright only drives employees towards unsanctioned solutions. Thus, the path forward lies in enablement combined with visibility and control.
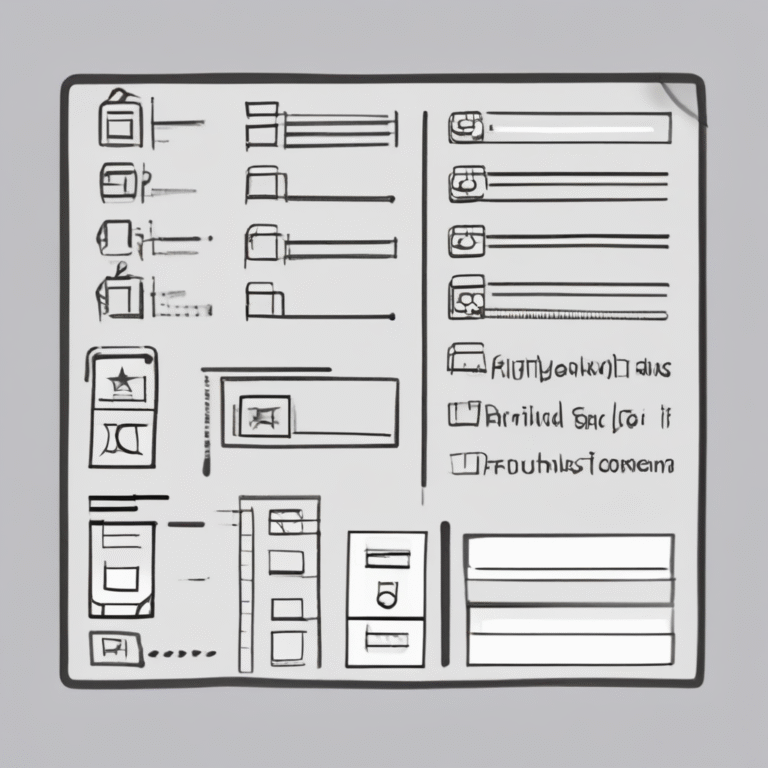
Effective GenAI governance requires context-driven visibility into:
- What data the enterprise possesses and where it resides
- Who has access to this data
- How GenAI is utilized across the organization
Organizations need to monitor tool access, prompt entries, and the flow of sensitive data in real-time. This can include flagging risky sessions, blocking unsanctioned tools, and implementing role-based restrictions on AI-driven insights.
In conclusion, GenAI represents a new layer of enterprise risk and opportunity. Managing this risk necessitates a paradigm shift, viewing security not as a barrier to innovation, but as the foundation that enables safe advancement.