Why AI Security Must Evolve Into Lifecycle Governance
Artificial intelligence now operates inside the core infrastructure of modern enterprises. AI models influence various systems including logistics networks, financial systems, fraud detection pipelines, and automated decision platforms. As these AI workloads expand across distributed environments, the security challenge is shifting. Protecting AI systems can no longer rely solely on reactive defense; organizations must secure the full lifecycle of these systems.
AI Governance as an Engineering Discipline
Cybersecurity researchers emphasize the need for security architecture to adapt to these changes. Treating AI governance as an engineering discipline rather than a mere compliance exercise is essential. AI systems behave as dynamic entities that require continuous monitoring, validation, and operational oversight. For security architects and cloud engineers, this means that they are not just securing infrastructure; they are also protecting data pipelines, model outputs, and the decision logic that increasingly drives enterprise operations.
AI Governance Becomes a Strategic Risk Category
The expansion of AI across enterprise systems has elevated AI governance into a board-level concern. Algorithmic systems now influence financial markets, logistics networks, healthcare operations, and other forms of critical infrastructure. As such, AI risk governance has become as important as financial and operational risks in enterprise oversight discussions.
Many organizations still apply traditional security models to AI environments. However, static compliance controls were designed for deterministic software, while AI models operate as probabilistic systems whose behaviors evolve. Effective AI risk management, therefore, necessitates lifecycle governance, extending security across data ingestion validation, training pipeline controls, secure deployment workflows, runtime monitoring, and continuous evaluation. In practice, enterprise AI security becomes part of the architecture itself rather than an external review layer.
The Expanding Attack Surface of AI Systems
AI introduces threats that differ from traditional cybersecurity vulnerabilities. For instance, model manipulation can occur through poisoned datasets, corrupted training signals, or adversarial inputs that distort predictions. Prompt injection attacks are also a growing concern, where generative models that interact with external systems can be redirected to produce unintended outputs or trigger automated actions.
To counter these threats, machine learning security strategies increasingly rely on autonomous AI security testing environments and structured AI red teaming exercises. These simulations enable organizations to test models against adversarial scenarios before deployment. Kanagala emphasizes that AI risk often centers on inference integrity rather than infrastructure compromise, meaning that systems may remain technically secure while their reasoning pathways become influenced by manipulated inputs.
Securing the AI Supply Chain
The security of the AI supply chain has become another critical focus area. Modern AI systems depend on complex dependency chains that include open-source libraries, pre-trained models, datasets, and cloud services. Without adequate validation mechanisms, organizations may deploy models with uncertain origins and training processes.
Researchers are exploring frameworks built around an AI software bill of materials (AI-SBOM). Similar to software supply chain documentation, this framework catalogs datasets, training pipelines, model artifacts, and dependencies. Keeping track of model provenance and integrity strengthens this approach, allowing organizations to verify where models originated, how they were trained, and whether components changed during deployment.
Zero Trust for Machine Identities
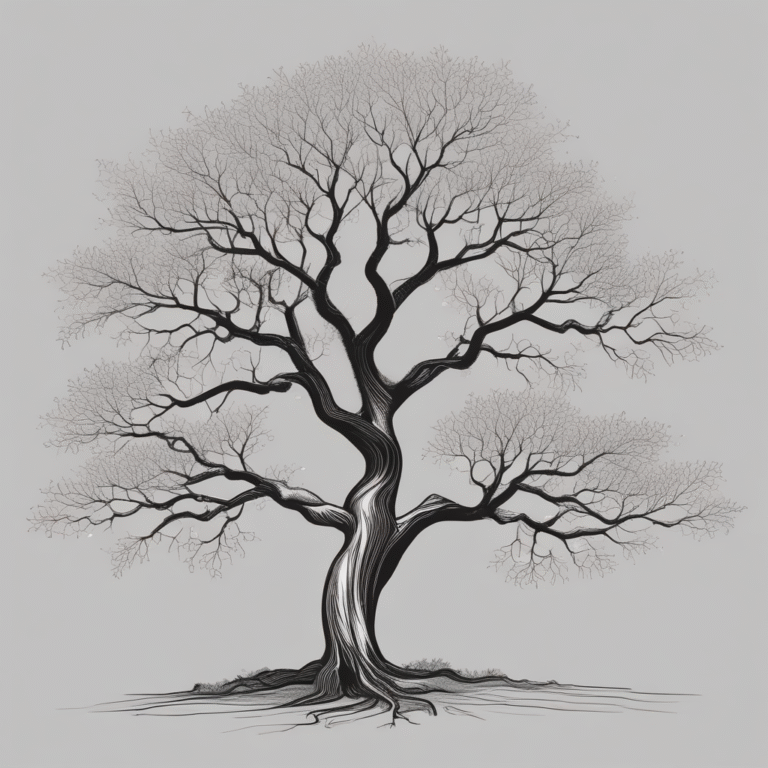
As AI continues to expand across distributed infrastructure, identity management becomes central to security architecture. A zero-trust architecture must extend beyond human users to include machine identities. Autonomous agents, model endpoints, orchestration services, and automated pipelines all require continuous authentication and authorization.
This approach ensures that every interaction between AI components is verified within modern cloud security architecture, supporting enterprise AI security across multi-cloud environments where data pipelines and models operate across multiple platforms.
Governance as Infrastructure
AI adoption is accelerating across various industries, making it essential to integrate AI infrastructure security, cloud risk management, and responsible AI implementation directly into engineering workflows. Organizations that adapt will build systems designed for resilience, while those that treat AI governance as an afterthought risk introducing systemic fragility into the digital systems that increasingly shape modern economies.