Identity-first AI Governance: Securing the Agentic Workforce
As AI agents increasingly operate within production systems — querying databases, updating customer relationship management software, and executing business logic autonomously — issues of governance and security have come to the forefront. This article explores the concept of identity-first AI governance and the importance of securing the agentic workforce.
The Governance Risks of Shared Credentials
In many enterprises, AI agents authenticate using static API keys or shared credentials instead of distinct identities within the corporate Identity Provider (IDP). This approach introduces significant governance risks. When an agent performs an action, logs often attribute it to a developer key or service account rather than a clearly defined autonomous actor, creating ambiguity in attribution.
Such ambiguity weakens the principle of least privilege, making it challenging to revoke access. Revocation may require rotating credentials or modifying code, which slows down investigations and containment efforts in a non-deterministic environment.
The Problem of Shadow Identities
Shared credentials effectively transform autonomous systems into shadow identities, operating within production environments without a governed identity in the enterprise directory. Although organizations typically have monitoring and guardrails in place, these autonomous systems often exist outside first-class identity governance.
Non-Deterministic Systems and Governance Considerations
Unlike traditional enterprise software that follows predefined logic, agentic AI systems operate differently. These systems utilize probabilistic models to:
- Evaluate context
- Retrieve information dynamically
- Construct action paths in real-time
This flexibility allows agents to solve complex, multi-system problems that traditional software cannot address. However, it introduces new governance considerations, such as:
- Execution paths may vary from one request to the next.
- Retrieved data sources may differ based on context.
- Outputs can contain reasoning errors or inaccuracies.
- Actions may extend beyond explicit developer instructions.
Why Credential-Based Security Falls Short
Many enterprises still secure AI agents using static API keys or shared service credentials. This model worked for predictable logic but breaks down in autonomous systems across production environments. When an agent authenticates with shared credentials, activity is logged but not attributed clearly, further complicating governance.
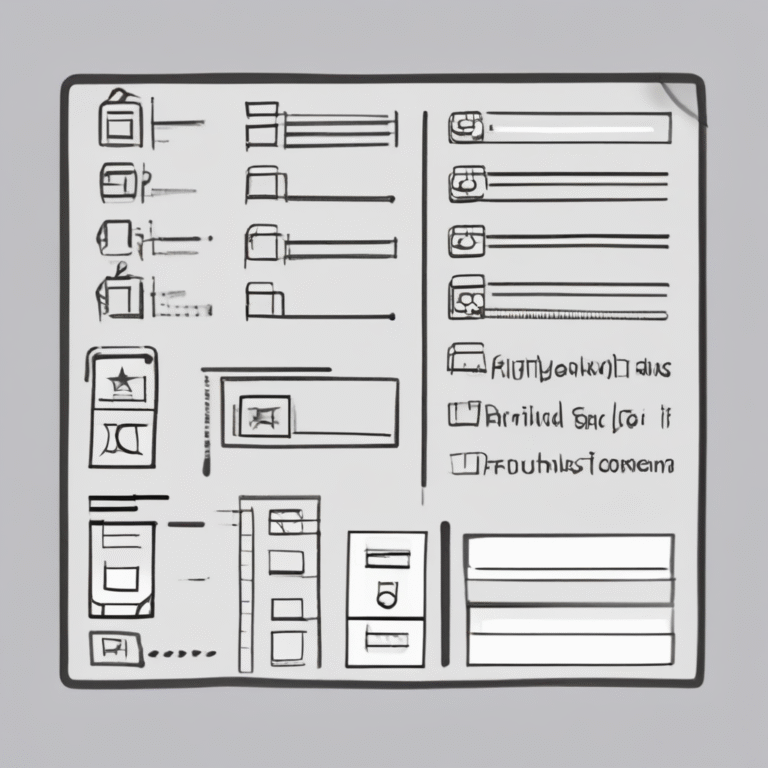
The Strategic Shift: Identity-First Governance
To address the governance gap created by shadow identities, organizations must adopt a structural shift in governance models. Identity-first governance treats autonomous systems as first-class identities within the same directory that governs human users. Each agent is assigned a distinct identity, scoped permissions, and auditable activity attribution.
This shift changes the control model significantly. Access becomes tied to identity rather than static credentials, and actions are logged to specific actors. Permissions can be adjusted without modifying code, and revocation occurs at the identity layer.
Practical Example: Identity-Backed Agents
One architectural response to the identity governance gap is to provision autonomous systems as first-class identities within the corporate directory. For instance, through a partnership between DataRobot and Okta, organizations can provision agents from the DataRobot Agentic Workforce Platform as governed identities directly in Okta.
In this model, each agent receives a directory-backed identity. Authentication occurs through short-lived, policy-controlled tokens instead of long-lived credentials embedded in code. Actions are logged to specific autonomous actors, and permissions are scoped using existing least privilege controls. This approach helps to resolve attribution and revocation challenges.
Three Governance Principles for Agentic AI
As autonomous systems transition into production environments, explicit governance becomes crucial. At minimum, organizations should adhere to three principles:
- Eliminate static credentials: Autonomous systems must authenticate through short-lived, policy-controlled credentials tied to a governed identity.
- Audit the actor, not the platform: Security logs should attribute actions to specific autonomous identities for effective investigation and anomaly detection.
- Centralize revocation authority: Security teams must be able to restrict or disable an autonomous system through the primary identity control plane.
Conclusion: AI Governance is Workforce Governance
As agentic systems become integral to core workflows, the need for robust governance models tailored for autonomous systems is evident. If a system can act, it must exist as a governed identity within the same control plane that secures human users. This identity-first approach lays the foundation for effective attribution, least privilege enforcement, continuous monitoring, and centralized revocation.
By integrating agent orchestration platforms with enterprise identity providers, organizations can extend their existing identity infrastructure to encompass autonomous systems, ensuring that governance scales alongside innovation.