Astrix Advances AI Agent Security Platform to Govern Shadow and Enterprise Agents
Astrix Security has revealed a major expansion of its AI agent security platform, covering every layer where AI agents operate in the enterprise. This includes managed AI platforms and shadow deployments running on managed devices. The platform is designed to detect both agent existence and unauthorized access to enterprise resources, enforcing policy over what agents are allowed to do.
The Challenge of AI Governance
AI governance programs are struggling to keep pace with the rapid deployment of AI agents. Existing governance processes operate on review cycles measured in weeks, while agents can be deployed in minutes. By the time a review is concluded, an agent may already be operational, accessing critical systems without any security review, leaving organizations vulnerable.
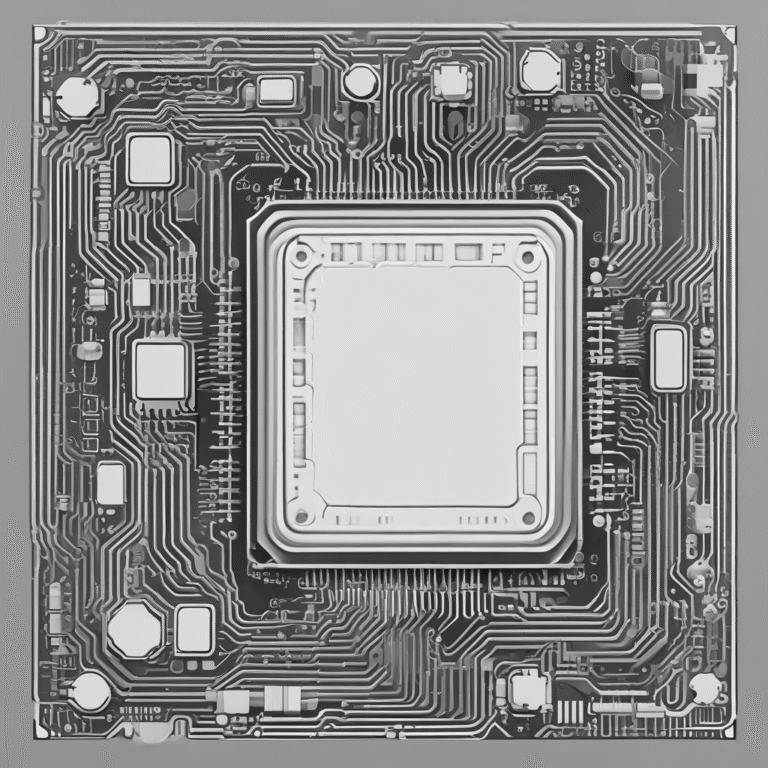
Comprehensive AI Agent Discovery
Astrix’s four-method discovery architecture is crafted to surface every AI agent—both sanctioned and shadow—along with MCP servers and non-human identities (NHI) across the enterprise stack. This architecture provides the context needed to assess the risk associated with each agent.
Method 1 — AI Platform Integrations
Astrix connects directly to AI platforms across the enterprise, revealing every registered agent and MCP server. This covers all major categories of agentic infrastructure, including:
- Enterprise AI assistants and copilots
- Cloud-native AI services
- Developer agent frameworks
- Agentic automation platforms like Microsoft Copilot, Amazon Bedrock, Google Vertex, OpenAI, and Salesforce Agentforce.
Method 2 — NHI Fingerprinting
Even unregistered agents leave traces. Each agent authenticates using an NHI such as an OAuth app, service account, API key, or PAT. Astrix monitors the NHI layer across cloud infrastructure, identity providers, SaaS platforms, and DevOps tools, detecting agents from the credentials they utilize. This identity layer serves as a definitive record of what an agent can access.
Method 3 — Sensor Telemetry
Astrix reads from endpoint detection and response systems (EDRs) such as CrowdStrike, SentinelOne, and Microsoft Defender, as well as network sensors. This method enables detection of agents that never connect to platform integrations, including locally-running agents within IDEs.
Method 4 — Bring Your Own Service (BYOS)
For proprietary or non-standard services, BYOS extends discovery beyond the catalog, ensuring no agent or service falls outside the inventory.
These four data sources feed into the Astrix Platform, mapping every discovered AI agent and MCP server to the NHIs it operates under, the credentials it holds, and the resources it can access. Risk is scored automatically, and remediation is prioritized based on access scope and blast radius.
Agent Control Plane (ACP): From Visibility to Enforcement
Understanding agent existence is insufficient. Astrix has enhanced its Agent Control Plane (ACP) with Agent Policies, a real-time policy engine that allows security teams to control AI agent actions. Teams can define “allow, flag, and block” rules scoped by user, department, agent platform, and resource type. Policies are evaluated before any action executes, ensuring unrecognized agent activity is flagged.
The Importance of Agent Control
Idan Gour, President of Astrix Security, emphasizes the urgency of this issue: “Shadow AI agents are not a theoretical problem. Before security knows an agent exists, it already has access to sensitive data and production operations.” This highlights the critical need for organizations to manage both agent discovery and enforcement effectively.
A complete agent inventory and real-time policy controls establish a foundation for enterprise AI productivity. Without visibility into the agents they have and governance over their actions, enterprises cannot determine which agents to trust or how to scale AI deployments effectively.