Artificial intelligence is rapidly transforming our world, presenting both unprecedented opportunities and complex challenges. Ensuring its responsible development and deployment requires a comprehensive understanding of the potential risks and the strategies to mitigate them. This analysis delves into the core principles that should guide the creation of effective AI risk mitigation, exploring how these principles translate into actionable steps throughout the AI lifecycle, from initial data collection to ongoing monitoring and maintenance. It also examines how the degree of openness in AI models influences the effectiveness of these strategies, highlighting the need for adaptable and nuanced approaches.
What are the underlying principles guiding the development of effective AI risk mitigation strategies
The Institute for Security and Technology (IST) emphasizes five guiding principles for crafting effective AI risk mitigation strategies. These principles acknowledge the rapid evolution of AI and the diverse perspectives needed to govern it responsibly.
The Guiding Principles:
- Balancing Innovation and Risk Aversion: Strive for responsible innovation. Prioritize identifying, assessing, and mitigating risks to align AI development with safety, ethics, and trustworthiness.
- Shared Responsibility: Engage all stakeholders—policymakers, AI developers, users, and civil society—in collaborative risk mitigation efforts. Each group’s unique perspectives and expertise are crucial.
- Commitment to Accuracy: Focus on developing AI models that provide reliable, factual information. Avoid censorship, factual alteration, or compromising truth to achieve desired outcomes.
- Practicable Regulation: Ensure regulatory oversight considers technical feasibility. Collaborate with AI experts and stakeholders to implement effective and technically achievable mechanisms.
- Adaptable and Continuous Oversight: Develop regulatory frameworks that keep pace with technological advancements. Incorporate mechanisms for regular review, refinement, continuous monitoring, and oversight.
These principles, resulting from extensive discussions with working group members, aim to foster a balanced, collaborative, and proactive approach to AI governance. They acknowledge the need for adaptable, feasible, and continuously evolving regulatory frameworks and oversight mechanisms. IST recognizes the importance of fostering innovation while prioritizing safety and ethics.
Applying the AI Lifecycle Framework in accordance with these guiding principles ensures targeted, feasible, and actionable interventions throughout AI development and deployment.
What methodology was employed to analyze malicious use risks within the AI landscape
IST began its analysis of malicious use risks by first examining overarching trends of these malevolent behaviors, ignoring the use of AI technology, in order to build an understanding of the ecosystems and behavioral patterns that surround each category. Second, it examined the current status of malicious use of AI technologies in each category to determine how these new AI technologies are being applied to existing behavioral patterns. Third, and finally, IST adopted a future-facing approach, to determine how, with extant and more advanced technologies, AI tools might be applied to each category.
The aim was to establish a clear historical context for each malicious use case so that analysts and policymakers could then overlay AI systems into the mix. Understanding both the historical and current patterns of malicious behaviors enables predictions about the future – specifically, how AI systems may fit into, or exacerbate, existing patterns of malicious activity.
Specific Malicious Use Risk Categories
The report identified five key risks that fall under the umbrella of malicious use, examining each using the methodology described above:
- Fraud and other crime schemes enabled by AI-generated social engineering content, particularly when targeting at-risk populations.
- Undermining social cohesion and democratic processes through targeted disinformation campaigns.
- Human rights abuses by expanding the ability of authoritarian states to surveil, constrain, and oppress minorities and dissidents.
- Disruption of critical infrastructure by providing malicious actors with offensive cyber capabilities.
- State conflict by contributing to the capabilities of adversarial or revanchist states looking for advantages in conflict.
How does the AI Lifecycle Framework address specific malicious use risks
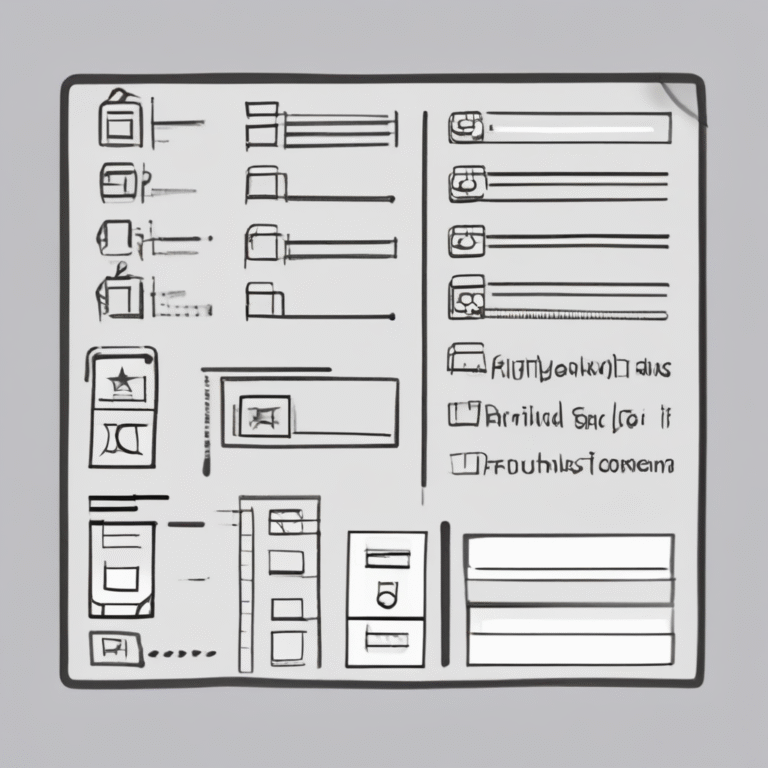
The AI Lifecycle Framework tackles malicious use risks by dividing the AI development process into seven stages, allowing for targeted interventions at each point.
Here’s how it works, with examples of risk mitigation strategies:
Data Collection & Preprocessing
This stage focuses on sourcing and preparing data. The framework suggests requiring transparency in data sourcing for large labs to prevent the use of unethical data. It also involves implementing rigorous data validation and sanitization protocols to remove anomalies that could skew the model towards malicious applications. Employing privacy-preserving AI techniques like federated learning further minimizes the risk of data exploitation.
Model Architecture
Here, the framework advocates for creating incentives for secure AI development and sharing best practices among leading labs and researchers. This helps prevent the theft of IP and leading models which can enable state conflict by providing adversarial states access to leading AI models. Providing legal protections and reward programs to whistleblowers for identifying unethical or malicious behavior within AI organizations protects against intellectual property theft or malicious data sets being employed.
Model Training & Evaluation
The priority shifts to detecting vulnerabilities. The framework suggests mandated regular security audits and penetration testing of AI training environments. It also advises setting up bug bounty programs to find and fix vulnerabilities. Red teaming, including adversarial testing, helps simulate malicious use scenarios and address any identified weaknesses.
Model Deployment
This stage emphasizes continuous monitoring. The framework recommends using machine learning techniques to detect intrusion or misuse in real-time. Anomaly detection mechanisms should be built into the model architecture, with alerts set up for potential misuse.
Model Application
Safeguarding against autonomous malicious actions is key. The framework mandates human oversight and control, especially in high-risk applications. Placing restrictions on the types of applications that can use foundation models reduces the likelihood of AI being used for malicious purposes through widely available commercial services. It’s also critical to conduct red team testing to identify and address vulnerabilities.
User Interaction
Existing legal measures should be leveraged to address misuse. Users who use AI to commit crimes should be held liable under existing criminal law, allowing enforcement agencies to act immediately against criminal behavior instead of waiting for specific AI related laws to pass.
Ongoing Monitoring & Maintenance
Maintaining vigilance is crucial. The framework emphasizes establishing clear reporting mechanisms for suspected fraud or malicious use. These mechanisms should be well-publicized and regularly reviewed. Additionally, continuous monitoring using machine learning helps detect and respond to threats in real-time.
By addressing risk at each stage, the AI Lifecycle Framework strives for a balance. It encourages innovation while minimizing harm, acknowledges shared responsibility among stakeholders, commits to accuracy, and promotes practical regulation with continuous oversights.
At which points of the AI lifecycle are risk mitigation strategies most crucial
As AI technologies rapidly evolve, understanding where to implement risk mitigation strategies within the AI lifecycle is paramount. Central to the AI Lifecycle Framework are seven distinct stages: data collection and preprocessing, model architecture, model training and evaluation, model deployment, model application, user interaction, and ongoing monitoring and maintenance.
Identifying effective intervention points requires acknowledging the nuances of “upstream” versus “downstream” risks and mitigations:
- Upstream Risks: These are inherent to the model itself, stemming from its training and development.
- Downstream Risks: These emerge from user interactions with the model.
- Upstream Mitigations: Strategies targeting model development and pre-deployment training.
- Downstream Mitigations: Strategies focused on model release, fine-tuning, application development, and user interaction.
The AI Lifecycle Framework helps ensure that risk mitigations are technically feasible, actionable, and targeted, aligning with core principles of AI governance. This approach necessitates the involvement of diverse stakeholders, enabling precise, informed choices that protect innovation while effectively reducing risks.
Data Collection & Preprocessing
High-quality data is paramount for training efficient AI models. Poor data quality can lead to biased or inaccurate models, reducing AI application effectiveness. In this stage, risk mitigation includes:
- Dataset Sourcing Transparency: Require large labs to reveal dataset origins, promoting ethical data usage.
- Data Validation and Sanitization: Use protocols to detect and remove suspicious data points.
- Privacy-Preserving AI Techniques: Employ federated learning and secure multi-party computation to protect sensitive data.
Model Architecture
A well-designed architecture is key to AI model performance, scalability, and security. Focused strategies include:
- AI Roundtables: Support forums for researchers to share best practices.
- Robust Security Standards: Enforce security standards for leading labs to protect intellectual property.
- Cash, Compute, or Grant incentives: Provide to researchers involved in collaborative projects aimed at sharing knowledge and best practices in secure AI development.
- Legal Protections and Reward Programs for Whistleblowers: Implement strong legal protections to report unethical or malicious use of AI technologies within organizations.
- Privacy-Preserving AI Techniques: Employ federated learning and secure multi-party computation to protect sensitive data.
Model Training & Evaluation
Rigorous training and evaluation are vital for reliable AI models, helping to address overfitting, underfitting, and biases. Mitigation efforts should Include:
- Regular Security Audits and Penetration testing: Mandate to identify vulnerabilities.
- Strong Legal Protections and Reward Programs for Whistleblowers: Implement strong legal protections to report unethical or malicious use of AI technologies within organizations.
- Bug bounty programs: Create bug bounty programs to identify weaknesses in known methodologies.
- Red Teaming: Conduct to simulate and identify potential malicious use scenarios.
Model Deployment
Effective deployment ensures AI models are utilized effectively. Risk mitigations here should consider:
- Strong Legal Protections and Rewards Programs for Whistleblowers: Implement strong legal protections to report unethical or malicious use of AI technologies within organizations.
- Continuously Monitor with machine Learning Techniques: Employ machine learning to detect intrusion.
- Anomaly Detection and Continuous Monitoring in Model Architecture: Implement for real-time identification of malicious activities.
Model Application
Impactful application development guarantees proper AI technology use. Focused mitigations include:
- Human Oversight and Control Mechanisms: Mandate for high-risk use cases to prevent fully autonomous malicious actions.
- Restrictions on Use of Foundation Models: Enforce restrictions on application types via developer agreements and app store policies.
- Red Team Testing: Conduct to simulate and identify potential malicious use scenarios.
User Interaction
Positive user interactions are crucial for AI technology adoption. Mitigation should focus on:
- Legal Measures: Prosecute users who misuse AI tools.
Ongoing Monitoring & Maintenance
Continuous monitoring ensures long-term AI system reliability and safety. Critical risk interventions are:
- Reporting Mechanisms: Establish accessible channels to report fraud and misuse.
- Public Campaigns: Ensure public awareness of reporting mechanisms.
- Confidentiality and Protection for Reporting Sources: Protect individuals who report suspected issues.
- Regular Review: Update reporting mechanisms based on feedback and technological advancements.
- Continuously Monitor with machine learning techniques: Employ techniques to detect and monitor for potential misuse.
Targeting these lifecycle stages with well-defined policy and technical interventions forms the cornerstone of a resilient AI risk management strategy.
How do openness considerations in the AI sector influence the effectiveness of various risk mitigation efforts
Openness in the AI sector significantly impacts the effectiveness of risk mitigation efforts. As AI models become more open, risks increase but so do opportunities for collaborative solutions. Policymakers and developers must recognize that different strategies become more or less relevant across the openness spectrum. Let’s dive in.
Openness and the AI Lifecycle Framework
The level of openness at each development stage introduces unique risk mitigation challenges.
- Data Collection & Preprocessing: Open models benefit from diverse datasets, which can reduce biases, but raise questions about data source ethics. Is the data ethically sourced?
- Model Development & Training: Openness here fosters transparency and collaboration, but enforcing security and ethics is more complex.
- Testing & Validation, Deployment & Monitoring, Maintenance & Governance: Open models necessitate community-driven (vs. centralized) oversight. How do you maintain security with distributed control?
The degree of openness affects both the risks and the possible remedies at each stage of AI development.
Openness and Mitigation Effectiveness
Some risk mitigation strategies become more challenging—or imperative—depending on the level of AI model openness.
- Use Case Restrictions: Difficult to enforce on fully open models due to easy access and modification, making centralized control almost impossible. The open nature of a model can severely limit the use of certain mitigations.
- Responsible Data Collection: Critical across all levels. Regardless the degree of openness, model training data must be representative and free from bias/malicious content. How can we ensure data veracity throughout the development process?
Consider a high level of openness, which can elevate malicious use risks. This occurs because malicious actors can access model components, and modify/fine-tune the model for harmful purposes. To counteract this requires strong security architectures, and robust testing/validation.
Practical Implications
When implementing risk mitigation strategies, follow these guidelines:
- Avoid superficial measures: Ineffective mitigations detract from credible recommendations. Prioritize robust, actionable strategies.
- Targeted interventions: Apply precise, informed choices to protect innovation while mitigating risks effectively.
- Dual approaches: Use both policy and technical interventions. Policy measures provide guidance while technical mitigations address specific risks at each stage.
By following these recommendations, AI stakeholders can develop and implement risk mitigation strategies tailored to the degree of openness. This effort aims to foster an environment where open access AI is developed ethically.
Ultimately, crafting effective AI governance demands a multifaceted approach. It requires embracing a balanced perspective, fostering transparency throughout the AI lifecycle from data acquisition to ongoing maintenance, and recognizing the imperative of both technical and policy interventions. Prioritizing adaptable, feasible, and consistently updated frameworks, supplemented by robust stakeholder collaboration, equips us to navigate the evolving landscape of AI risks while simultaneously nurturing responsible innovation. This ensures that as AI capabilities advance, societal benefits are maximized, and potential harms are proactively minimized.